Faust is a perl script that helps to analyze files found after an intrusion or compromised. Its goal is not to make the analysis, but to extract the pieces of information to html report that you will use afterward in your analysis. This tool is seldom mentionned anywhere but I would like to give it a try on my CentOS system. Faust requires certain dependencies and I need to install it to get it run.
Installing it's dependencies - ltrace and strace
shell>yum install ltraceSetting up Install Process
Setting up repositories
update 100% |=========================| 951 B 00:00
base 100% |=========================| 1.1 kB 00:00
addons 100% |=========================| 951 B 00:00
extras 100% |=========================| 1.1 kB 00:00
Reading repository metadata in from local files
primary.xml.gz 100% |=========================| 75 kB 00:04
update : ################################################## 185/185
Added 4 new packages, deleted 4 old in 0.82 seconds
Parsing package install arguments
Resolving Dependencies
--> Populating transaction set with selected packages. Please wait.
---> Downloading header for ltrace to pack into transaction set.
ltrace-0.3.36-2.EL4.i386. 100% |=========================| 5.5 kB 00:00
---> Package ltrace.i386 0:0.3.36-2.EL4 set to be updated
--> Running transaction check
Dependencies Resolved
======================================================
Package Arch Version Repository Size
======================================================
Installing:
ltrace i386 0.3.36-2.EL4 base 72 k
Transaction Summary
======================================================
Install 1 Package(s)
Update 0 Package(s)
Remove 0 Package(s)
Total download size: 72 k
Is this ok [y/N]: y
Downloading Packages:
(1/1): ltrace-0.3.36-2.EL 100% |=========================| 72 kB 00:09
Running Transaction Test
Finished Transaction Test
Transaction Test Succeeded
Running Transaction
Installing: ltrace ######################### [1/1]
Installed: ltrace.i386 0:0.3.36-2.EL4
Complete!
[root@trinity FAUST-0.1.0rc2]# yum install strace
Setting up Install Process
Setting up repositories
update 100% |=========================| 951 B 00:00
base 100% |=========================| 1.1 kB 00:00
addons 100% |=========================| 951 B 00:00
extras 100% |=========================| 1.1 kB 00:00
Reading repository metadata in from local files
Parsing package install arguments
Resolving Dependencies
--> Populating transaction set with selected packages. Please wait.
---> Downloading header for strace to pack into transaction set.
strace-4.5.13-0.EL4.1.i38 100% |=========================| 12 kB 00:00
---> Package strace.i386 0:4.5.13-0.EL4.1 set to be updated
--> Running transaction check
Dependencies Resolved
======================================================
Package Arch Version Repository Size
======================================================
Installing:
strace i386 4.5.13-0.EL4.1 base 91 k
Transaction Summary
======================================================
Install 1 Package(s)
Update 0 Package(s)
Remove 0 Package(s)
Total download size: 91 k
Is this ok [y/N]: y
Downloading Packages:
(1/1): strace-4.5.13-0.EL 100% |=========================| 91 kB 00:04
Running Transaction Test
Finished Transaction Test
Transaction Test Succeeded
Running Transaction
Installing: strace ######################### [1/1]
Installed: strace.i386 0:4.5.13-0.EL4.1
Complete!
After all the needed dependencies by faust get installed, you will have to tweak the variable path of the binaries in faust.conf, I will show the only part I have tweaked and I'm running CentOS 4.2.
objdump /usr/bin/objdump
strings /usr/bin/stringsreadelf /usr/bin/readelf
ldd /usr/bin/ldd
nm /usr/bin/nmltrace /usr/bin/ltrace
strace /usr/bin/strace
md5sum /usr/bin/md5sum
#ps /bin/ps
#awk /bin/awkYou config may be vary, just define properly and it's done, now should be time to run faust.
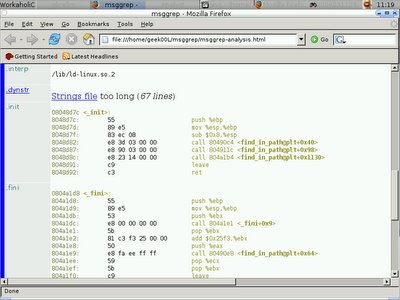
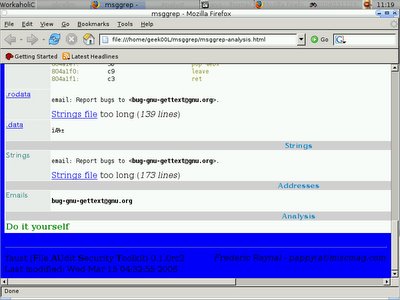
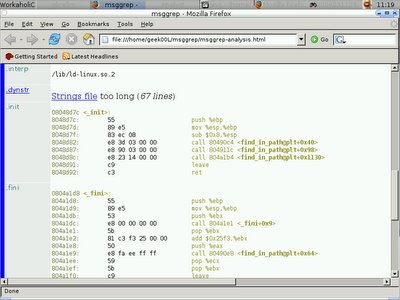
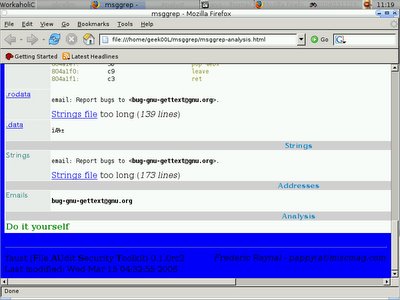
shell>faust.pl -c faust.conf msggrepOnce it runs without errors, it will generate the html file called msggrep-analysis.html with it's corresponded directory.
Modifying the generated html report since it shows the page with black color background and black color text so we see nothing, just edit bgcolor variable will do. You may modify faust.pl since it's more easy for later.
body bgcolor="blue"
table cellspacing="2" bgcolor="white" border="0" cellpadding="0" width="100%"
table cellspacing="1" bgcolor="white" border="0" cellpadding="0" width="90%"And don't forget to copy faust.css file since it is already been included in the generated html file.
You can download faust at
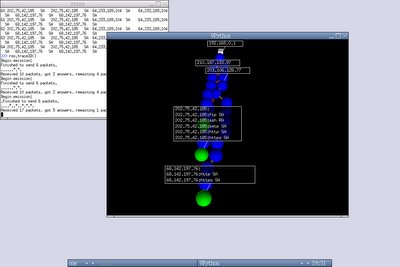
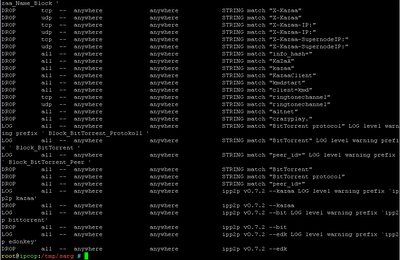
http://security-labs.org/index.php3?page=faustHere's the output example -


 Cheers :]
Cheers :]