IDS used to suffer in high speed network where it need to sustain the heavy load traffics while detecting malicious traffic. Relying solely to the IDS software seems not to be a right idea, hence OS tweaking is supposed to be done in order to build a perfect Intrusion Detection System with commodity hardware, of course gigabit network card is preferred with lots of RAM. Here's my current testing configuration and I hope this is helpful to certain people who want to run IDS with comodity hardware and using either Bro-IDS or Snort. The OS I'm running is FreeBSD, you may find similar tweaking with Linux.
I added this to kernel config file in order to enable device polling,
options DEVICE_POLLING
options HZ=1000
After recompile the kernel and install it, I added those values below to the /etc/sysctl.conf
net.bpf.maxbufsize=8388608
net.bpf.bufsize=4194304
net.inet.tcp.sendspace=65536
net.inet.tcp.recvspace=65536
net.inet.tcp.rfc1323=1
Then I added this configuration to /etc/rc.conf for the network interface that used to capture network traffic and running IDS as well.
ifconfig_fxp1="polling promisc up"
I suggest if you are running IDS with commodity hardwares, you may need two network interface, one will be the management interface with access control enabled and another one just run as IDS interface, the configuration above applies to the IDS interface where IP is not needed and no other traffics inteference except the traffic you want to capture.
I'm currently testing how well this experimental IDS box in heavy load traffic, I run snort in sniffer mode,
shell>snort -i fxp1 -D
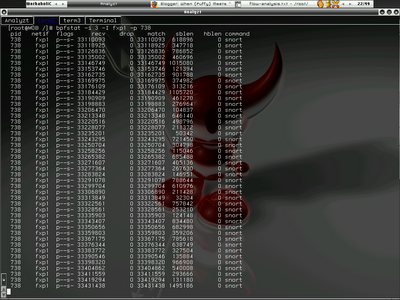
My snort PID is 738, since I have bpfstat installed, I try to run -
shell>bpfstat -i 3 -I fxp1 -p 738
You can view the result in the screenshot, 0 drop rate .....
If you happenned to know the better tweaking of OS or you are actually performing tweaking for your IDS box in different kind of OS as well, please do feedback or comment. I would like to learn more ways of building IDS boxen with commodity hardware.
Cheers (:])
1 comment:
Where did you get the values for /etc/sysctl.conf from?
Post a Comment