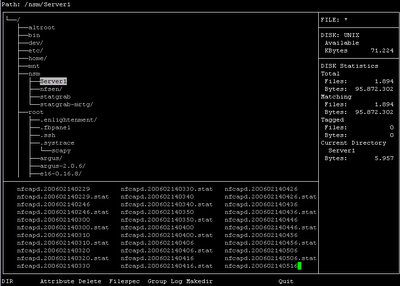
I just found this nifty curse base file manager that is available in OpenBSD port/package - Ytree. Ytree is very lightweight file manager, however it has all the features that supposed available in the file manager, I don't think it suits everyone's need because most people prefer a gui file manager, but you should check out this one. Ytree allows you to browsing the directory tree, copy, remove or rename files whenever you want, it also shows the file size and disk space info on the right pane, one of the reason I like it is that I can just run it when I ssh remotely to the terminal or the servers without X, many will say they can just use ls but once you get yourself handy with ytree especially when you comfortable with it's key command, you can navigate all the files easily with Ytree. The other thing is that you can even execute the command directly while you are still browsing your file manager and get back to your file manager once you have finished the execution, the argument of the command can be changed on the fly as well.
The only con I found would be the problem where I can't navigate to the the previous parent directory, what I mean is that if I start running Ytree at /usr, I only can browse through all the file unders /usr and can't go to / or /home and etc, so I have to start running Ytree at / which is the root of the system that allows me to navigate all the files.
The only con I found would be the problem where I can't navigate to the the previous parent directory, what I mean is that if I start running Ytree at /usr, I only can browse through all the file unders /usr and can't go to / or /home and etc, so I have to start running Ytree at / which is the root of the system that allows me to navigate all the files.